Basic module
Your basis for first-class information security
Sometimes information security feels like a maze of shortcuts, processes and requirements. Don’t worry, we are your GPS. With our basic module, we bring structure, security and clear paths into your IT world. Even if it is possible to work without a structured security strategy, we ask a simple question: why take the risk? Our solutions are the key to protecting against threats, meeting regulatory requirements and building trust with customers, partners and employees.
The basic module is not just an option. It is the foundation for a stable and future-proof security strategy. Information security is not a luxury, but an investment in the stability, reputation and long-term success of your company. Contact us and find out how easily and effectively security can be implemented.
What does the basic module include?
- Chief Information Security Officer (CISO)
- Information Security Management System (ISMS)
- Implementation project
- Information security full-managed service
- Professional training courses
Chief Information Security Officer (CISO)

A central component of the basic module is your personal Chief Information Security Officer, or CISO for short. This experienced expert focuses exclusively on a small group of customers, including you. Your CISO will become a constant in your company by providing strategic support in the development and implementation of security measures. Their knowledge and availability will ensure that your information security strategy is always up to date. In emergencies, be it a cyber-attack, a last-minute audit request or an internal security breach, your CISO is ready to respond quickly and effectively. You could, of course, try to fill this role internally, but why miss out on a proven solution that’s ready to go?
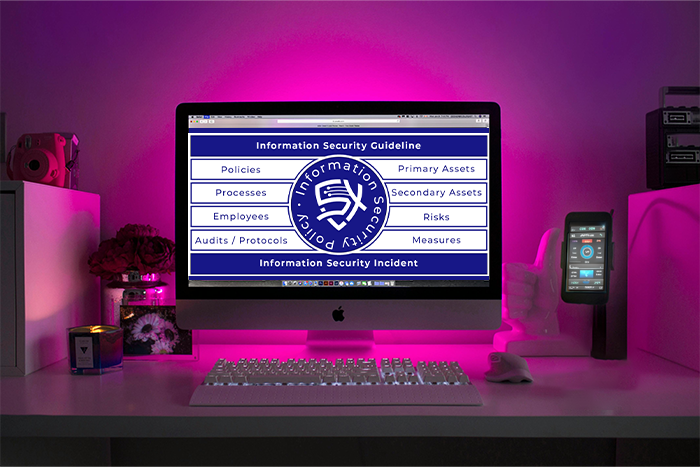
Information Security Management System (ISMS)
The technical core of the basic module is our Information Security Management System (ISMS). Based on Q.Wiki, one of the most modern tools for management systems, the ISMS is precisely adapted to the requirements of your company. It is not an unnecessarily complex tool, but a system that integrates seamlessly into your existing processes. With an ISMS, you not only have a tool that is prepared for certifications such as ISO 27001 or TISAX, you also create a central system that ensures transparency, identifies risks at an early stage and continuously optimizes your security measures. You can work without an ISMS, but remember: a clearly documented and audited system is not only more efficient, but also saves costs and effort in the long term, especially in the event of audits or customer inquiries.
Implementation project

To ensure a smooth start to your ISMS, we support you with a clearly structured implementation project. Our experts take the time to understand your existing processes and design the changeover in such a way that it remains clear and comprehensible for everyone involved. This is not a standard process, because we develop a solution for you that suits your company. An implementation without support would be possible, but why take the risk of wasting valuable time and resources? With us at your side, you save time, avoid common pitfalls and ensure that the implementation is a success right from the start.
Information security full-managed service
Once an ISMS has been introduced, the challenge remains to maintain and continuously develop the security measures. Our fully managed service takes on this task for you. We take care of identifying your most important corporate assets, carry out regular risk analyses, develop tailor-made measures and integrate them into your processes in a sustainable manner. We also support your employees in implementing security guidelines, raise their awareness of risks and make information security an integral part of your day-to-day work. Of course, you could try to manage all of this internally, but remember: with us, you have experts at your side who can implement these tasks routinely, efficiently and in line with best practices. The result? A higher level of security, less internal stress and more freedom to concentrate on your core business.

Professional training courses

An often underestimated component of information security is the professional training of your employees. We can help you identify the right people to take on responsibility as information security officers or local information security officers in your company. These training courses are not only technically sound, but also practice-oriented, so that participants receive the tools and knowledge to create real added value for your company. Without such training, your security strategy will be ineffective, because in the end, success depends on the competence and commitment of your employees. With us at your side, you can be sure that your team is in the best possible position.